In 2024, the Federal Communications Commission fined AT&T, Verizon, and T-Mobile a combined $200 million for selling customer location data without authorization.
That same year, AT&T suffered a breach that exposed the call records of more than 100 million Americans, roughly one third of the US population.
The data included not just phone numbers, but a detailed map of who those people called, when, and from where.
For Cape, a privacy-focused mobile carrier, those headlines were not a surprise. They were the reason the company exists.
The company owns its own mobile core, the software layer that controls how calls are routed, what data is collected, and how long it is retained. That distinction, Cape argues, is the difference between genuine privacy and marketing language.
The company’s approach is technical and deliberate. It rotates subscriber identifiers daily, making continuous tracking significantly harder. It protects phone numbers with a BIP 39 seed phrase, the same standard used by Bitcoin hardware wallets, meaning no customer service representative, and no Cape employee, can reassign a number without the account holder’s authorization.
It has also built a proprietary firewall against SS7 signaling attacks, a class of network-level exploit that operates beneath the reach of any VPN.
Cape has attracted early adopters from the cryptocurrency community, but the company says its ambitions are broader. It has offered free service to domestic violence survivors, partnered with Proton for encrypted email and cloud storage, and made its service compatible with GrapheneOS out of the box.
We spoke with Ruddy Wang, Cape’s Head of Customer Growth, about what your carrier actually knows about you, why most privacy tools stop short of the network layer, and what it takes to build a telecom from the ground up with privacy as the foundation.
The full conversation follows.
Heather: I just interviewed Rudy Wang, head of customer growth at Cape. Now, you’ve worked at Uber, Meta, and also Spenmo. What drew you specifically to Cape, which is a mobile carrier focused very deeply on privacy?
Ruddy: Cape is a really interesting company because it stretches across all these different boundaries in all these different sectors. From my prior experience, I have experience in fintech, consumer businesses, etc. Cape is one of the few places that has a consumer, enterprise, and government business, which is really rare. It speaks to the fact that full connectivity is relevant across all the different aspects of our lives — in many good ways, but while we’ve been making this change, we have unknowingly given up a lot of privacy. A lot of us love the convenience. We love being able to call an Uber. We love being able to watch an Instagram video on the way to work, but we’ve never consciously made the decision that in doing this, we are allowing ourselves to be tracked and allowing our data to be leaked or breached. This isn’t a case where you’re going to Walmart and your Walmart data is breached. When your telecom data is breached and sold, that tells people almost everything about your life — where you go, people you know, and things like that. I just thought that mission was really interesting and relevant to the way technology has developed today. That’s what brought me here.
Heather: I think people are unaware of exactly what information the carrier is leaking. You are getting location data. How much sensitive information are we leaking, or specifically what is it?
Ruddy: That’s a good question. If you think about what kind of information is available to your carrier — obviously there’s your location. In order for your cell phone to work, your telecom carrier needs to know where you are to connect you to the closest cell phone tower. Once somebody has your location, they know where you sleep at night. They know where you go during the day — where you go to work, your place of worship, where all your doctors are. If your kids go to school and you pick them up, they know that, and they’ll know your entire routine.
The other thing is there’s a record of every single person you’ve called or texted. Most of us, even if we’re using encrypted chat apps like WhatsApp or Signal, are still calling our aunt, our school, getting phone calls from the doctor’s office. Your entire social graph can be elaborated, and someone can see the top 10 people in your life — which is really useful for all sorts of attacks and social engineering. They can also know IP addresses and whether you’re using a VPN or a particular service.
In 2024, the FCC fined AT&T, Verizon, and T-Mobile $200 million for selling customer location data in ways they weren’t supposed to. Also in the same year, AT&T was breached by hackers who got access to the call logs of over 100 million Americans — that’s like a third of the US population. All those call logs go back years and years.
Heather: Somebody could look at where you were two years ago today based on that information. That’s just incredibly powerful. We’re used to hearing about data breaches now, but when you think of a data breach with a telecom, it’s a different kind. It’s not like a Walmart data breach where they have some of your shopping data. It’s a data breach of your entire life. That’s very sobering, Rudy. As head of consumer growth — is Cape primarily targeting Bitcoiners or high-net-worth individuals, or is this a path to mass market adoption as people become more aware of how much their privacy is in danger?
Ruddy: Our goal has always been mass market adoption. I think it’s relevant for everyone, but the people who have been our early adopters and most interested are particularly people in the crypto community — for a couple of reasons. One is that if you’re in crypto, you’re more targeted. The second is that when you’re in crypto, you’re probably already a little more privacy- and security-aware, and also more tech-forward.
One example is our SIM swap protection. Our protection against SIM swaps is different from what you’d find with any other carrier. It works like a crypto wallet — you get a seed phrase, and nobody can change your SIM to any other phone without that seed phrase. Normally, SIM swap attacks happen when somebody social engineers a customer support rep at Verizon, saying, “Hi, I’m Heather, but I just got a new phone. Please switch my phone number to this new phone.” Once they have that phone number, they have what they need to hack into accounts and steal your crypto. The way we do it is that without the seed phrase, that number can’t be changed to a new phone. No Cape customer support rep, no Cape engineer can switch a phone number from one phone to another. Only the subscriber can do so. It’s a concept the crypto community is very familiar with — cold wallets, for example. They end up becoming a lot of the early adopters in this space because they’re so familiar with this kind of technology. It’s been around in crypto for a while, but in the world of telecom, this level of security is new.
Heather: Anytime you’ve lost your PIN or password, you’re just locked out and the carrier is trying to protect you against a SIM swap. But it’s going to be a single point of failure in the same way — once you lose that seed phrase, you’re locked out. Do you just start over? Has that happened yet?
Ruddy: That has happened, and it’s pretty tough. We can’t really help people there, but it’s part of the security model. We’re exploring other ways to make it easier on folks as well, but your community would know — that’s the most secure model. Your seed phrase is your phone number in this case.
Heather: Using BIP 39 — it’s the same standard as Bitcoin hardware wallets. Your target audience is familiar with that, and our target audience is familiar with that. Did you do this purely as a technical decision, or because you specifically wanted to target Bitcoiners and the crypto community?
Ruddy: It’s relevant to everyone. We definitely had the crypto community in mind, but there are also stories of entire families having their bank accounts drained because there’s still a surprisingly large number of banks and financial institutions where you have to give a phone number as an authentication method. There are social media accounts that still require a phone number. We’ve seen cases of celebrities having their social media accounts hacked, then fraudulently promoting a particular crypto coin. The use case for not wanting your phone number stolen is pretty broad, because it’s still today the number one authentication factor — not just for crypto accounts, but for other financial accounts, your social media account, all sorts of things.
Heather: Everything got attached to our phone number and we were asleep at the wheel about it. I saw that before the recent rollout, Cape actually rolled out service to some victims of domestic violence — people I would count as non-technical. How did they work with BIP 39, with the seed phrase concept — this language Bitcoiners are familiar with but a less technical audience might not be? Were they able to grasp using a seed phrase and going this new route?
Ruddy: We started getting messages from people saying, “I’m a domestic violence survivor. I’d like to get your service.” At that point, we weren’t offering service to the public yet, but we definitely wanted to accommodate that. We give the service for free, but we also don’t feel like we’re the entire solution. If someone is being stalked by a technically sophisticated partner, there are other issues we’re not well-placed to address. We list a number of partner resources and we partner with an organization called Safe Escape, led by Chris Cox. They work with survivors to lock down their digital life — they can help on laptops, and for phones, through them we’re able to offer service wrapped up in a context where someone can help with all the more sophisticated technical aspects.
That said, we have lots of people signing up for Cape now who are not from the crypto space, and we’ve tried to make it very user-friendly. You have multiple reminders to save your seed phrase. It’s very easy to copy and save it to a password manager. You have to retype your seed phrase so that you’re not forgetting it. There are things we’re doing to make onboarding easier.
Heather: Do you accept Bitcoin or Lightning payments for Cape subscriptions at all? And if not, is that on the roadmap?
Ruddy: We get that question a lot. We have a lot of folks in the space who want to pay with Bitcoin and other crypto, but we don’t accept crypto right now. It’s definitely something we’re looking into and would love to offer in the future, but I don’t have a specific date.
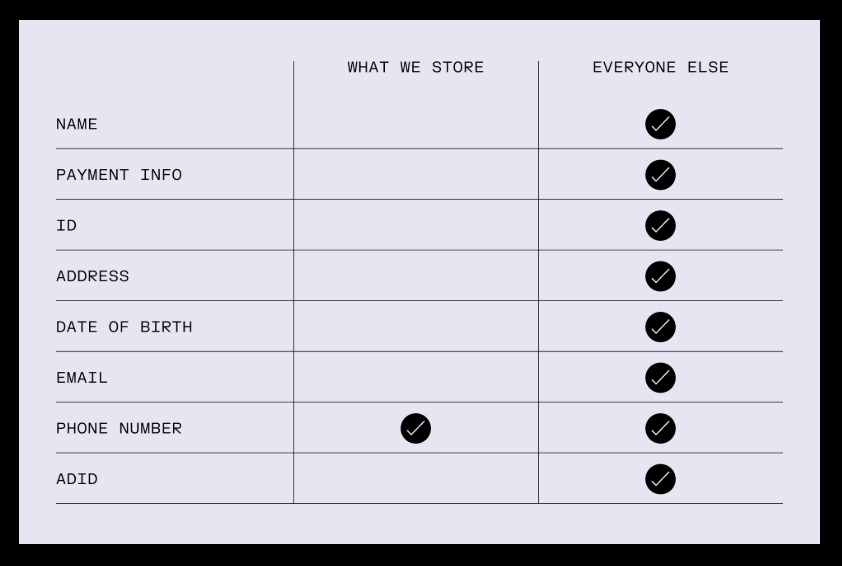
What people want is for their identity not to be tied to their phone number, their phone account, and all their phone activity. What we offer right now is we separate that data. We use Stripe as our payment gateway, which is pretty normal in the e-commerce space but extremely rare in the telecom space. Traditional telecoms — Verizon, etc. — all have systems called BSSs, or business support systems. These are huge legacy systems that require keeping all customer addresses, credit card numbers, etc. on their own systems. When you move to a modern payment gateway, we don’t keep that information. Stripe just gives us a randomized token. Even if we were hacked, even if somebody within Cape wanted to get customer information, they wouldn’t be able to — they’d just get that randomized token. You can pay with a prepaid card, etc. There are various options right now to sign up for service in a more anonymous way, but we’re always trying to improve. We’ve got lots of demand for a way to pay with crypto, so that’s definitely something we’re looking into.
Heather: I did not know that about Stripe. That’s amazing. Now, a lot of Bitcoiners are skeptical of anything they might perceive as “centralized.” How do you address that “trust me bro” concern where you’re asking people to route their calls through your network and trust you as this new thing they may think of as just another carrier?
Ruddy: One of the big things we have to do is build trust. The main way we try to do that is by being as transparent as possible. If you go to our privacy policy, we have the most plain-language privacy policy in the industry. We tell you exactly what data we collect and how long we keep it for. If you go to a Verizon privacy policy, you’ll see hundreds of pages, and when you try to find out how long they keep your location data, it says “as long as necessary to serve the purposes of this privacy policy” — which is another way of saying they’ll keep it as long as they want.
In our privacy policy, we show exactly the information that is kept and exactly how long it’s kept. Separately, we also have a Trust Center that gives real-time information about our security posture. You can download past audits there. We’re currently trying to figure out a way to audit and prove our short data retention — we retain call metadata, what are called CDRs or call logs, for only one day, rather than five years.
We’re looking for an external audit for that so we have additional external proof that this is happening. We’re open to suggestions, and that’s something we’ll be doing soon.
Heather: Can people view that audit on GitHub or GitLab, or is that something you’re going to post on the website?
Ruddy: It’s all undefined right now. We want to make it as accessible as possible, so we’re still looking at options.
Heather: Our readers at Lightning News would be familiar with the privacy angle. A lot of people say to jailbreak or unlock a phone, make sure it’s an Android, and put GrapheneOS on it. That seems to be the option in the community, though it means you have to be highly skilled — it’s the developer route. I believe on your website it was mostly Google or Android phones. It seems like you guys know what GrapheneOS is. What kinds of phones are available?
Ruddy: GrapheneOS is a more secure OS. The reason we started looking into it more is that a lot of our early subscribers were GrapheneOS users. When you have a specific OS, every cellular network is going to interact differently with it. Once we realized we had a whole bunch of folks interested in GrapheneOS, we knew we had to put more technical work in so that it was a first-class service — all the MMS messages are working, all the calls are working. There is work that needs to be done to make a network compatible with that, and we did that.
We also made Cape available in the Crescent Store, which is a privacy-first app store. You don’t need to go through Google at all to download it. That was another big ask from the community.
It doesn’t take a huge amount of work to install GrapheneOS, but if you’re not technical at all, it might feel a little scary. We still advise people they can install it themselves, but if they don’t want to, we also offer Pixel devices with GrapheneOS pre-installed in our store. It just removes a little bit of that friction, given how much demand there’s been in our community.
Heather: So you can go quite private and you don’t have to do the work yourself.
Ruddy: We try to make it easier. Privacy has always been sacrificed for the sake of other types of convenience. The way to remedy that is to make privacy convenient — to make sure you don’t have to make some major compromise in order to be more private and lose a huge amount of functionality. The whole concept here is that you sign up, you get premium service, you get nationwide coverage, you get everything you’d expect from regular premium 4G/5G service, but it’s more private and secure, and you’re not compromising tons of usability for that.
Heather: Which is actually really impressive — more than I imagined, honestly. I’m one of those people who wouldn’t use GrapheneOS because I’m not going to bother with it. I’m just dealing with the cell carrier plan I bought.
Now, another thing you guys are doing with Cape, which our audience would be familiar with, is the Proton partnership. A lot of us use Proton, and you’ve bundled together encrypted email, VPN, and cloud storage with Proton. Is this the vision of being a one-stop privacy stack, or is the focus on mobile? You also talked about working with Safe Escape — you’ve got these partnerships going to keep everything ultra-private.
Ruddy: When somebody comes to a service like ours, or to privacy-first services like Proton, often they’ve had some sort of incident — they’ve been scammed, or had a scary experience where it feels like they’re getting creepy ads, or feels like they’re being followed or tracked in some way, and they don’t exactly know where the threat vector is coming from. When they come to a particular service, they just want to know: can you solve all my problems?
We focus specifically at the cellular network level because we believe that’s where a lot of the problems lie and where there are essentially no solutions. There are lots of app-level things — VPNs, encrypted chat apps — but at the cellular network level, because you need to build a huge amount of infrastructure, there’s essentially no solution in the space. That’s where we’ve come in and filled this gap.
Because everybody needs a cell phone plan — and your typical T-Mobile, Verizon, AT&T plans are going to bundle Hulu and Netflix — our vision is that people who want more privacy and security can come to Cape and see more and more of their problems holistically addressed. That’s why it made a lot of sense to partner with Proton. They’ve got email, VPN, Drive, a whole bunch of services that when put together really expands the value to the customer. We also had a huge amount of alignment with them in terms of values. We’ve had a great experience working with them to educate people more about privacy and make it more accessible.
Heather: You mentioned Cape owns its mobile core. Can you explain what that means practically and why it matters for security, and how it differentiates you from other choices?
Ruddy: Owning a mobile core means we own all the software infrastructure it takes to run a telecom, and that’s extremely important because that is how we provide our privacy and security features. If you don’t have your own mobile core, many of the decisions about what data is collected by the network and how calls and SMS are routed are outsourced to one of the major carriers — T-Mobile, Verizon, AT&T.
We’re the only carrier in the world that is privacy-focused, owns our own mobile core, and has all our traffic running through it. You’ve probably heard of a lot of other telecoms that have popped up — there’s Mint Mobile, Boost Mobile, Mr. Beast announced he’s launching a mobile carrier, a whole bunch of other celebrities launching mobile carriers, Kroger the grocery store has their own wireless service. All of those do not have their own mobile core. There’s what are called “light MVNOs,” which means they put some light marketing skin over the core infrastructure of other major telecoms. It’s very different for us.
For example, we’re able to offer services like network lock, which protects you from attacks. A signaling attack is when a compromised telecom says, “Hey, Heather, you are now roaming with us — please direct all call, SMS traffic, and location data to us.” That’s an incredibly powerful attack. If you look up “SS7 signaling attack” on YouTube, you’ll find videos showing how this works. It happens at the control layer of the telecom — think of it as the switchboard for where to route your calls, texts, SMS, and location data. We have a proprietary firewall there that protects against these types of attacks. It will deny any request from suspicious networks, and you can’t do that if you’re Mr. Beast Mobile.
Heather: And probably the Proton VPN I have on my phone right now, if I forget to connect it, it’s probably not going to protect me from that either.
Ruddy: A lot of these attacks happen at the network level, which is a layer below all the apps. In order for the apps you typically use to interact with the internet, it all has to carry over this cellular data connection. That’s the layer we’re really focused on.
Heather: I tend to turn my VPN off when an app stops working. I go, “It’s the VPN,” turn it off for a few minutes, and then I often forget to turn it back on. Is there any sacrifice in service for having this increased level of security that Cape provides?
Ruddy: No. We’re providing premium service. You get nationwide data — not only nationwide data, but in over 50 countries you get international data roaming included in the plan. All the top countries Americans would typically travel to are covered. There’s 4G and 5G coverage. There’s basically all the basic functionality, but we make it all a little more secure.
For example, voicemail — not that a lot of people use voicemail nowadays — but our voicemail is actually encrypted on our server. There are attacks in which the attacker gets your OTP sent to your voicemail, and once they’ve hacked the voicemail, they get your OTP. For us, this has to be decrypted on device using the private key on your device. You get all the baseline stuff, but every piece of it we try to make a little more private and secure.
Heather: I could see this becoming more in demand from people outside of this highly technical world. Do you know what percentage of mobile users would be projected to demand this Cape level of privacy or security as their default in the next few years?
Ruddy: We can look at the adoption of other things. You’ve mentioned VPNs a lot. VPNs used to be very niche. A lot of people didn’t know what they were. Now nearly one in three Americans use a VPN. You’ll see VPN commercials on prime time TV and it’s very well known. I think it’s the same in the mobile plan market. Right now it’s niche because nobody knows another option exists. You have to sign up for a cell phone plan; you have to go with one of the traditional carriers because they control 99% of the market. That’s just the deal if you want to be connected.
Once another option exists, it will follow the same trend, and there will be a third of the American population who just thinks, “I want to be tracked less. I’m not comfortable giving up so much of my privacy just to participate in the modern internet world.” That desire becomes more and more strong as you think about AI and other technological developments. Privacy is becoming more relevant, not less.
Heather: Ruddy, everybody’s got a chatbot they’re talking to on their phone right now with their Telegram or Signal. Is there a security angle there that Cape helps with? There have been some questions about these AI bots and how they’re not very secure.
Ruddy: It’s very much an evolving thing. I use AI — it’s convenient in both professional and personal life — but it also introduces a lot of potential security and privacy vulnerabilities, and we haven’t discovered them all yet. There’s going to be a lot more that comes out over the years. We want to leverage AI for good. There are a lot of areas in which AI can be leveraged — for example, handling spam and a whole lot of other things that would be prohuman — but it’s still early.
Interviewer: It’s still very early. Okay, Rudy, two more quick questions. This is great stuff today. It’s about time somebody provided this level of security, and certainly spotlighting what it can do for victims of domestic violence, journalists, and the privacy and security angle there. You guys have thought of a lot of different angles here in the audience you’re targeting and the tech you’re using. This is very unique.
You guys have a lot of funding at Cape, a lot of venture capital. Is the end goal acquisition by a major carrier, an IPO, or staying independent for the long term?
Ruddy: We’ve grown quickly. We don’t have any specific outcome in mind, but whatever outcome that is, what’s important is that the privacy promises we’ve made to our customers are respected and that continues. Within our privacy policy, it notes that if we did end up being acquired in any way, our privacy policy must remain respected as part of the terms of that deal. That’s the most important thing.
I don’t think we have a specific outcome in mind, but I do think we’re not a natural add-on to another company or service. Think about it — the reason that a lot of services are bundled onto phone plans is that everybody has to have a phone plan. It’s quite fundamental. We see ourselves as that fundamental baseline service, and it’d be hard for us to just be an appendage or attachment to some other technological service.
Heather: Now, for any Bitcoiners reading this — I’ll give you the floor, Ruddy — make the case for why Cape should be part of any Bitcoiner’s security stack alongside the obvious things we use: hardware wallets and multisig.
Ruddy: If you’re in crypto, you’re already aware of privacy and security and how the two are linked. The more information you can keep private about yourself, the less you are targeted. You’re already tech-forward in many ways — you’re using cold wallets, VPNs, other types of apps. But the one hole in your arsenal right now is at the cellular network layer. There hasn’t been another option. There is one now.
We’re able to keep things a lot more private. We rotate your IMSI — that’s your subscriber ID or identifier — every single day, so it’s hard to track you over time. You actually look like a different subscriber on the network every single day. You won’t find that kind of technology anywhere else, because it requires such a huge amount of investment in core mobile infrastructure.
Heather: I’m beginning to see where that VC capital is going. This stuff is not cheap. But your cell phone plan at $99 a month — that’s less than I’m paying right now. That’s actually pretty incredible. I’m going to have to take a deep look into this as a consumer and not just a tech nerd who wants to know the Bitcoin angle.
I appreciate your time, Rudy, because there have been a lot more conversations among friends and colleagues over the past year. We’ve seen a lot of SIM swaps, wrench attacks, kidnappings of people with crypto. We’ve seen some violence, and we’ve all been talking about how to improve OPSEC and how to go more private — little things you could tweak or actions you could take over time. Buying a gun, improving your self-defense, all different things. But nobody’s really talked about this angle yet: changing your cell phone carrier. There have been some options around for a few years, but this is something you guys have thought through from many different angles — what you call identifier rotation, the IMSI that you flip every day.
So if you’re a target in any way — whether you’re a journalist, activist, dissident, somebody who’s been a victim of stalking or violence of any kind — having that identity rotated is unique in this space. Is there anything else you wanted to add?
Ruddy: The last thing I’ll say is that technology — crypto itself — has brought a lot of great things to us. It’s also brought a lot of new threats. We’re really happy to be able to offer service that keeps people a little bit safer in this more digital and connected world, whether it be journalists and domestic violence survivors, or folks who are investing in crypto and are just trying to live their lives without becoming a target.
Heather: Very cool. I might know some people who definitely need to hear about you, especially working in this space. Thank you, Rudy. Thank you for your time and for being so gracious in answering all my questions today.
Ruddy: Thank you.